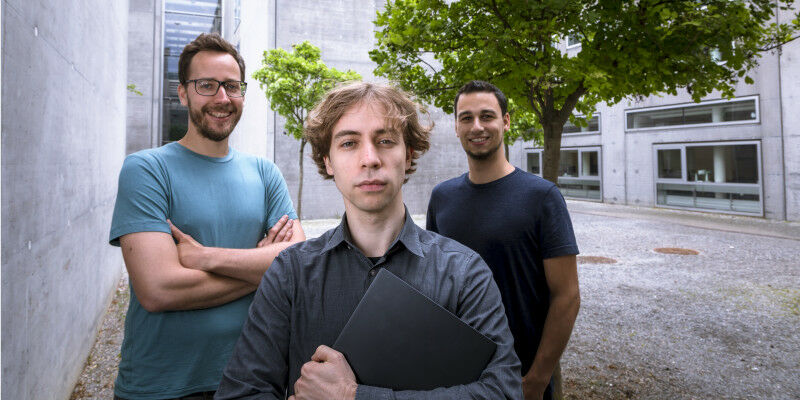
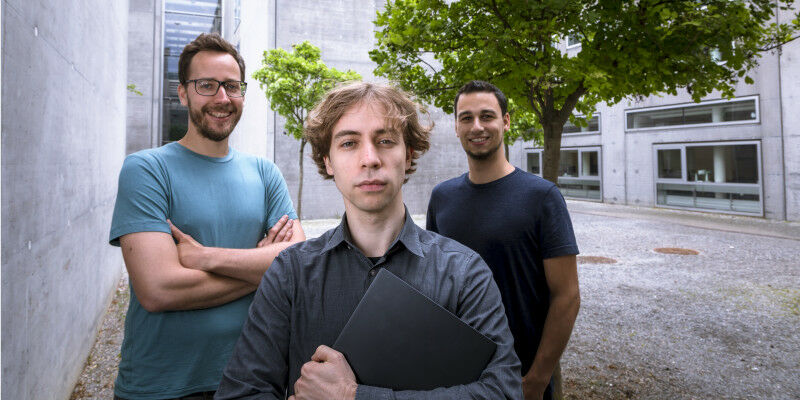
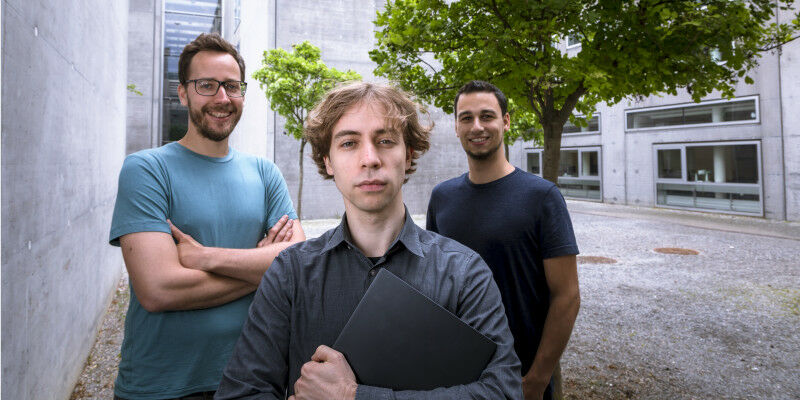
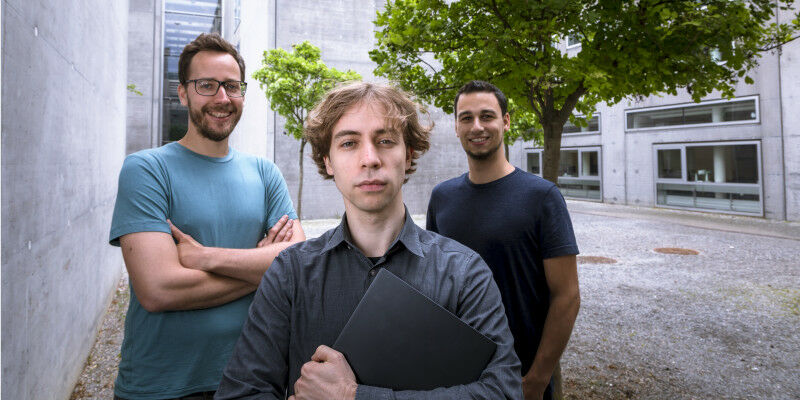
 Moritz Lipp, Daniel Gruss and Michael Schwarz were centrally involved in the discovery of Meltdown and Spectre.
Moritz Lipp, Daniel Gruss and Michael Schwarz were centrally involved in the discovery of Meltdown and Spectre.
By Birgit Baustädter - At the beginning of 2019, an international research team led by Daniel Gruss, Michael Schwarz and Moritz Lipp from TU Graz discovered the processor loophole ZombieLoad. Since then there has been a software patch and new processors. But with a new variant of the old attack these are no longer safe either. Meltdown and Spectre opened an entirely new security research area in early 2018. Until then, loopholes were sought for and found exclusively in the software of a computer system - but not in the hardware. That changed fundamentally with this new class of attacks. Since the discovery of these serious security problems, the team around Daniel Gruss, Michael Schwarz and Moritz Lipp have regularly published new security leaks.
TO READ THIS ARTICLE, CREATE YOUR ACCOUNT
And extend your reading, free of charge and with no commitment.
Your Benefits
- Access to all content
- Receive newsmails for news and jobs
- Post ads