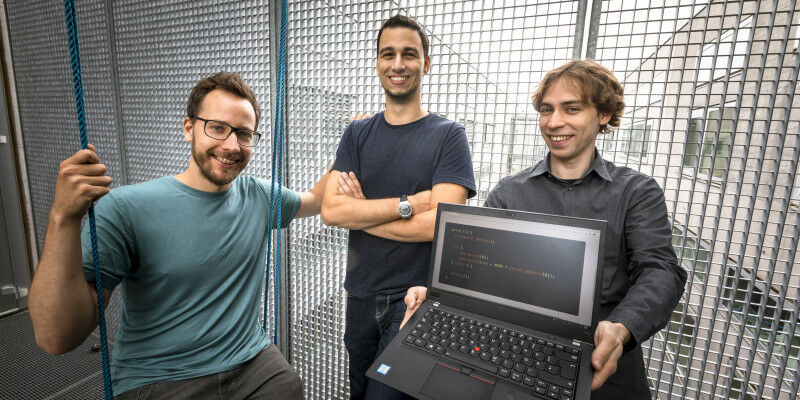
 Michael Schwarz (middle) with Moritz Lipp and Daniel Gruss - and the few lines of code that can be used to execute the ZombieLoad attack.
Michael Schwarz (middle) with Moritz Lipp and Daniel Gruss - and the few lines of code that can be used to execute the ZombieLoad attack.
Michael Schwarz ( middle ) with Moritz Lipp and Daniel Gruss - and the few lines of code that can be used to execute the ZombieLoad attack. Lunghammer - TU Graz By Birgit Baustädter - Michael Schwarz is a security specialist at Graz University of Technology and, together with colleagues, generated a completely new field of research a few years ago. An interview with the researcher. "We don't want to see the world burning, as many people accuse us of doing," clarifies Michael Schwarz with a laugh, over coffee in the institute kitchen. "We just want to make things safer." Michael Schwarz is a security researcher at the Institute of Applied Information Processing and Communications and part of the team that discovered the Meltdown and Spectre security vulnerabilities in 2017, thus opening up a completely new field of research. At that time a doctoral candidate under Daniel Gruss at TU Graz , he has now completed his PhD - albeit under special conditions. The contents of his thesis were still secret at the time of his thesis defence, as ZombieLoad 2.0 contained the latest security loophole which the researchers made public in November 2019 - two weeks after Schwarz graduated.
TO READ THIS ARTICLE, CREATE YOUR ACCOUNT
And extend your reading, free of charge and with no commitment.
Your Benefits
- Access to all content
- Receive newsmails for news and jobs
- Post ads